Risk Management
Santen strives to establish an information management and monitoring system in response to various risks, including unpredictable uncertainties, to eliminate such risks or address them appropriately.
Risk Management System
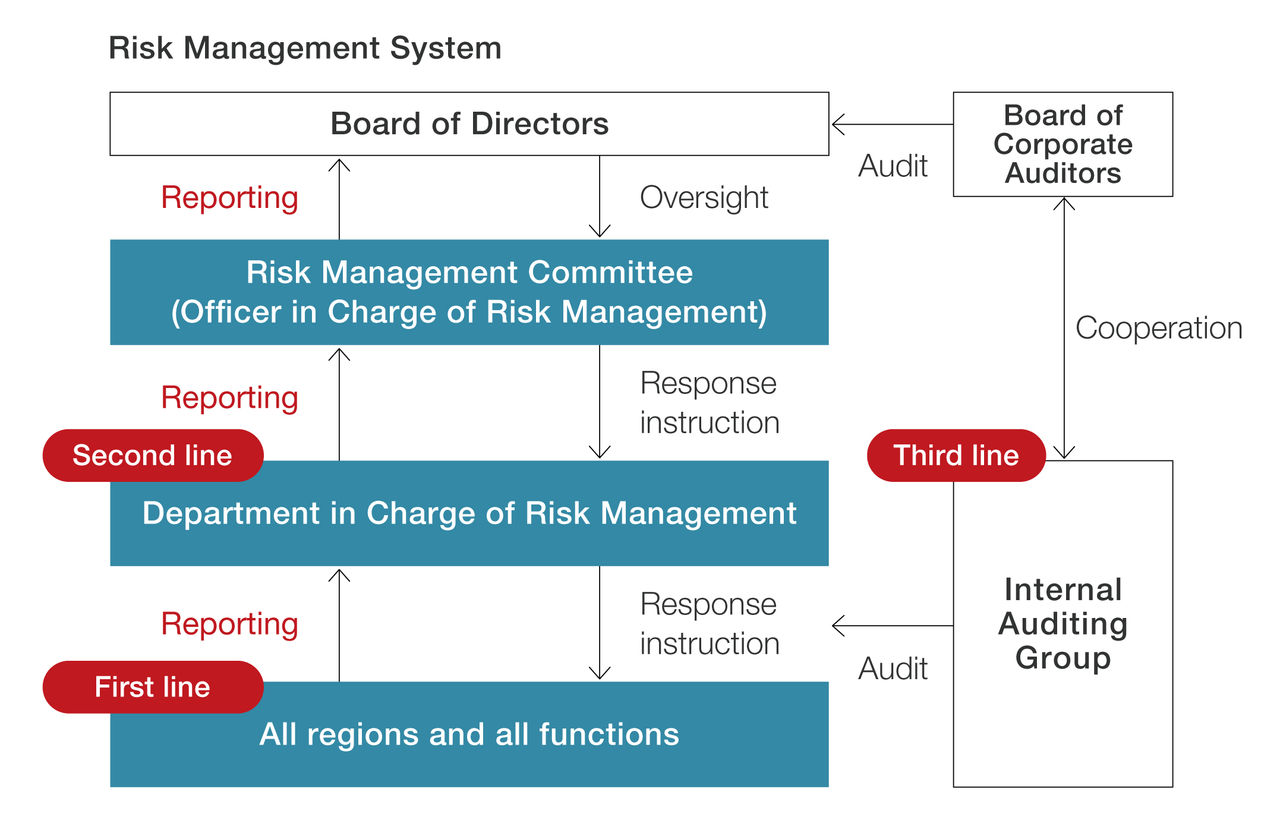
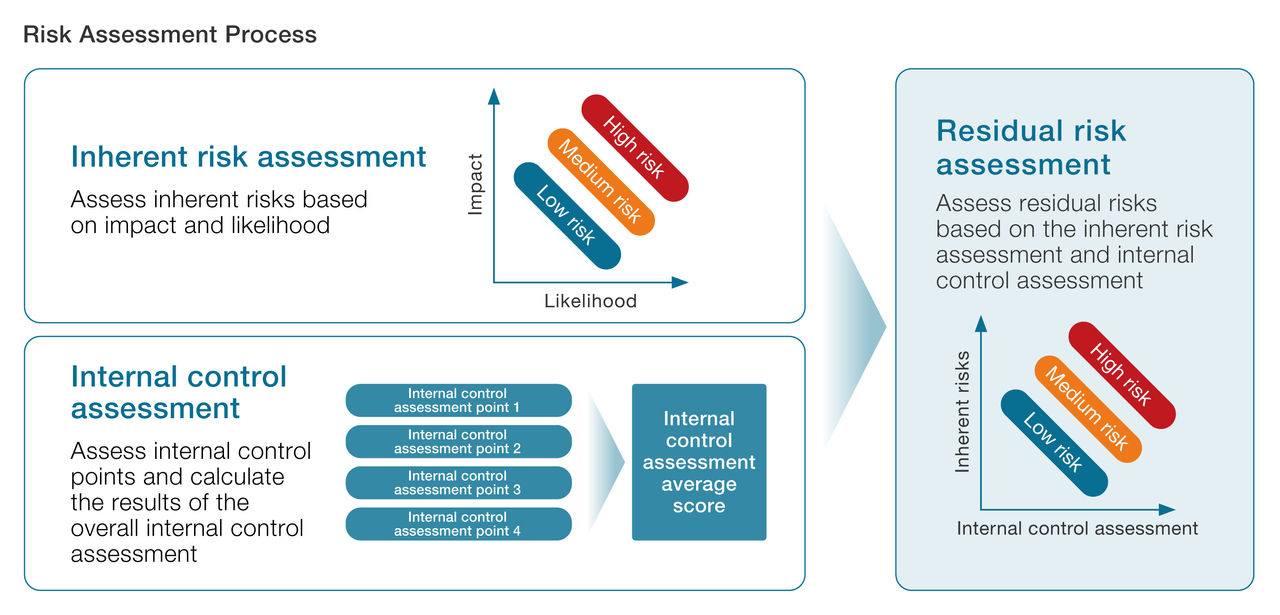
In accordance with the rules for risk management, we identify, evaluate, and monitor risks regularly in each region and division to deal with assumed major risks of loss related to the execution of our business activities, striving to avoid or minimize the risk of loss during times of normal business operations. To enhance risk management, starting from the FY2024, we will conduct interviews with each risk owner based on the Three Lines Model to confirm risk scenarios and assess ‘inherent risks.’ By evaluating ‘internal controls,’ we will calculate ‘residual risks’ annually. High residual risks will be identified as significant company-wide risks and will be deliberated by the Risk Management Committee to establish an effective enterprise-wide risk management system.
As our business expands globally, and we are required to comply with various regulations at higher levels, we must take appropriate measures to ensure the stable supply of products, quality control, IT security, and compliance, as well as to ensure management of risks such as pandemics, natural disasters, and conflicts.
To address the variety of risks that may affect our business in particular, we continue to strengthen risk management activities with preventive controls and activities that uncover potential risks under the leadership of the Officer in Charge of Crisis Management.
In its independent capacity, the Internal Auditing Group verifies the status of risk management through annual internal audits.
In the event or report of an event that has the potential to develop into a serious crisis, we form a crisis management committee, chaired by the Santen president and CEO. This committee responds to and contains the situation in question as we implement measures to prevent recurrence.
Major Risks
1) Supply chain
Risk scenario
Impacts on corporate value
Countermeasures and current progress
2) Compliance
Risk scenario
Impacts on corporate value
Countermeasures and current progress
3) IT Security and Information Management
Risk scenario
Impacts on corporate value
Countermeasures and current progress
4) Natural disasters
Risk scenario
Impacts on corporate value
Countermeasures and current progress
5) Geopolitical Risk
Risk scenario
Impacts on corporate value
Countermeasures and current progress
6) Risk related to Investment
Risk scenario
Impacts on corporate value
Countermeasures and current progress
7) Dependence on Key Products Risk Scenario
Risk scenario
Impacts on corporate value
8) Dependence on Licensed Products Risk Scenario
Risk scenario
Impacts on corporate value
Emerging Risks
We recognize emerging risks as those that have become particularly risky in recent years due to environmental changes and other factors.
1) International Disputes
Description
Impact
Countermeasures and current progress
Risk Culture
We strive to foster a risk culture throughout the organization. As part of these efforts, we provide in-house training on internal controls, compliance, and other topics via e-learning, and the training participation and other factors are included in the compensation evaluation of directors and employees. In terms of risk management, all relevant departments are involved in the evaluation of each risk. Furthermore, senior management discusses significant risks and their countermeasures in the Risk Management Committee, thereby promoting the formation of risk awareness.
When developing products and services, we analyze the relevance and risks at the development strategy and planning stages to consider risk mitigation. At the same time, we have the PTS Committee review and determine the Probability of Technical Success (PTS) of a project. In addition, we establish financial criteria to assess investment risk and determine business feasibility. We then perform development in accordance with the rules determined. Depending on the phase and monetary standards, the Board of Directors will discuss risks before making a decision on certain development and investment projects.